Amazon QuickSight is a scalable, serverless, embeddable, machine learning-powered business intelligence (BI) service built for the cloud. QuickSight lets you easily create and publish interactive BI dashboards that include Machine Learning-powered insights. QuickSight dashboards can be accessed from any device, and seamlessly embedded into your applications, portals, and websites.
QuickSight offers several sources for data, including but not limited to Amazonska Atena, Amazon RedShift, Preprosta storitev shranjevanja Amazon (Amazon S3), and Snowflake. This post presents solutions to enable you to set up Snowflake as a data source for QuickSight regardless of your network configuration requirements.
We cover the following configurations of Snowflake as a data source for QuickSight:
- QuickSight connection to Snowflake via AWS PrivateLink
- QuickSight connection to Snowflake via AWS PrivateLink and virtual private cloud (VPC) peering (same Region)
- QuickSight connection to Snowflake via AWS PrivateLink and VPC peering (cross-Region)
- QuickSight connection to Snowflake (public network)
Predpogoji
To complete this solution, you need the following:
- AWS račun
- O Vmesnik ukazne vrstice AWS (AWS CLI) installed on your workstation (for instructions, see (Installing, updating, and uninstalling the AWS CLI version 2)
- An Enterprise edition QuickSight account
- A Snowflake account
- A Snowflake database and table
- A Snowflake warehouse
- Zadosten AWS upravljanje identitete in dostopa (IAM) privileges to create VPC endpoints, security groups, route tables, and Amazonska pot 53 hosted zones and resource record sets
QuickSight connection to Snowflake via AWS PrivateLink
First, we show you how to connect to Snowflake with QuickSight over AWS PrivateLink. The following diagram illustrates the solution architecture.
Set up the Snowflake AWS PrivateLink integration
To start, we walk through enabling AWS PrivateLink for your Snowflake account. This includes locating resources in your AWS account, access to the Snowflake UI, and creating a support case with Snowflake.
- Identify the VPC you want to use to set up the AWS PrivateLink integration. To do so, retrieve a list of VPCs from the command line, then retrieve the
VpcIdelement from the resulting JSON object for the desired VPC. See the following code:
- Retrieve your AWS account ID. This post assumes that the account you’re targeting is your default account on your AWS CLI configuration.
- If you’re setting up multiple accounts, repeat these steps for all accounts and VPCs (this post assumes you’re setting up a single account and VPC and will use this as the context moving forward).
- Kontakt Snowflake Support with your AWS account ID, VPC ID, and the corresponding account URL you use to access Snowflake (for example,
<account id>.snowflakecomputing.com).
Enabling AWS PrivateLink for your Snowflake account can take up to two business days.
- After AWS PrivateLink is enabled, retrieve the AWS PrivateLink configuration for your Region by running the following command in a Snowflake worksheet, then retrieve the values for
privatelink-account-urlinprivatelink_ocsp-urlfrom the resulting JSON object. Examples of each value are as follows:
- Store these values in a text editor for later use.
Next, we configure the VPC endpoint on the Navidezni zasebni oblak Amazon (Amazon VPC) console create all the required security groups.
- Na konzoli Amazon VPC izberite Končne točke v navigacijskem meniju.
- Izberite Ustvari končno točko.
- Izberite Find AWS Service by Name.
- za Ime storitve, vnesite vrednost za
privatelink-vpce-idthat we retrieved earlier. - Izberite Preverite.
A green alert with “Service Name Found” appears and the VPC and subnet options automatically expand.
Depending on your targeted Region, your resulting screen may show another Region name.
- Choose the same VPC ID that you sent to Snowflake.
- Select the subnets where you want to create endpoints.
AWS recommends using more than one subnet for high availability.
- za Varnostna skupina, izberite Ustvarite novo varnostno skupino.
To odpira Varnostne skupine page on the Amazon VPC console in a new tab.
- Izberite Create security group.
- Give your new security group a name (for example,
quicksight-doc-snowflake-privatelink-connection) in opis. - Choose the VPC ID you used in previous steps.
Next, you add two rules that allow traffic from within your VPC to this VPC endpoint.
- Retrieve the CIDR block for your targeted VPC:
- Izberite Dodaj pravilo v Vhodna pravila
- Izberite HTTPS for the type, leave the source as po meri, and enter the value retrieved from the preceding
describe-vpcscall (for example, 10.0.0.0/16). - Izberite Dodaj pravilo v Vhodna pravila
- Izberite HTTP for the type, leave the source as po meri, and enter the value retrieved from the preceding
describe-vpcs - Izberite Create security group.
- Retrieve the security group ID from the newly created security group.
- On the VPC endpoint configuration page, remove the default security group.
- Search for and select the new security group ID.
- Izberite Ustvari končno točko.
You’re redirected to a page that has a link to your VPC endpoint configuration, specified by the VPC ID. The next page has a link to view the configuration in full.
- Retrieve the topmost record in the DNS names list.
This can be differentiated from other DNS names because it only includes the Region name (such as us-west-2), and no Availability Zone letter notation (such as us-west-2a).
- Store this record in a text editor for later use.
Configure DNS for Snowflake endpoints in your VPC
To configure your Snowflake endpoints, complete the following steps:
- On the Route 53 console, choose Hosted Zones v podoknu za krmarjenje.
- Izberite Ustvari gostujoče območje.
- za Domena, enter the value you stored for
privatelink-account-urlfrom the previous steps.
In this field, we remove the Snowflake account ID from the DNS name and only use the value starting with the Region identifier (for example, <region>.privatelink.snowflakecomputing.com). We create a resource record set later for the subdomain.
- za tiptako, da izberete Private hosted zone.
Your Region code may not be us-west-2; reference the DNS name returned to you by Snowflake.
- v VPCs to associate with the hosted zone section, choose the Region in which your VPC is located and the VPC ID used in previous steps.
- Izberite Ustvari gostujoče območje.
Next. we create two records: one for privatelink-account-url in enega za privatelink_ocsp-url.
- o Hosted zones stran, izberite Create record set.
- za Ime zapisa, enter your Snowflake account ID (the first eight characters in
privatelink-account-url). - za Vrsta zapisa, izberite CNAME.
- za vrednost, enter the DNS name for the Regional VPC endpoint we retrieved in the previous section.
- Izberite Create records.
- Repeat these steps for the OCSP record we notated as
privatelink-ocsp-urlearlier, starting withocspthrough the eight-character Snowflake ID for the record name (for example,ocsp.xxxxxxxx).
Configure a Route 53 resolver inbound endpoint for your VPC
QuickSight doesn’t use the standard AWS resolver (the VPC’s .2 resolver). To resolve private DNS from QuickSight, you need to set up Route 53 resolver endpoints.
First, we create a security group for the Route 53 resolver inbound endpoint.
- o Varnostne skupine page of the Amazon VPC console, choose Create security group.
- Enter a name for your security group (for example,
quicksight-doc-route53-resolver-sg) in opis. - Choose the VPC ID used in previous steps.
- Create rules that allow for DNS (Port 53) over UDP and TCP from within the VPC CIDR block.
- Izberite Create security group.
- Note the security group ID, because we now add a rule to allow traffic to the VPC endpoint security group.
Now we create the Route 53 resolver inbound endpoint for our VPC.
- On the Route 53 console, choose Inbound endpoint v podoknu za krmarjenje.
- Izberite Ustvari vhodno končno točko.
- za Ime končne točke, vnesite ime (npr.
quicksight-inbound-resolver). - za VPC v regiji, choose the VPC ID used in previous steps.
- za Security group for the endpoint, choose the security group ID you saved earlier.
- v IP naslov section, choose two Availability Zones and subnets, and leave Use an IP address that is selected automatically izbrano.
- Izberite Prijave se.
- Choose the inbound endpoint after it’s created and take note of the two IP addresses for the resolvers.
Connect a VPC to QuickSight
To connect a VPC to QuickSight, complete the following steps:
- o Varnostne skupine page of the Amazon VPC console, choose Create security group.
- Vnesite ime (npr.
quicksight-snowflake-privatelink-sg) in opis. - Choose the VPC ID used in previous steps.
Security groups for QuickSight are different from other security groups in that they are stateless, rather than stateful. This means you must explicitly allow return traffic from the targeted security group. The inbound rule in your security group must allow traffic on all ports. It needs to do this because the destination port number of any inbound return packets is set to a randomly allocated port number. For more information, see Vstopna pravila.
- Izberite Create security group.
- Take note of the security group ID, because we now add a rule to allow traffic to the VPC endpoint security group.
- o Varnostne skupine page, search for the security group ID that is used for the VPC endpoint.
- Izberite Uredite vhodna pravila.
- Add rules for both HTTPS and HTTP traffic, using the security group ID for the security group you created as the source.
- Izberite Shrani pravila.
Next, we move to the QuickSight console to configure the VPC connection.
- Pomaknite se do konzole QuickSight.
- Choose the user name and choose Upravljajte QuickSight.
- V podoknu za krmarjenje izberite Manage VPC connections.
- Izberite Add a VPC connection.
- za VPC connection name, vnesite ime (npr.
snowflake-privatelink). - za VPC ID, choose the VPC used in previous steps.
- za ID podomrežja, choose one of the subnets that has a VPC endpoint, as specified when you created the endpoint earlier.
- za Security group ID, enter the ID of the security group you created.
- za Končne točke razreševalnika DNS, enter the two IPs for the inbound resolver endpoint you created earlier.
- Izberite ustvarjanje.
Set up a Snowflake data source through the VPC
To set up a Snowflake data source, complete the following steps.
- Na konzoli QuickSight izberite Podatkovni nizi na navigacijski strani.
- Izberite Nov nabor podatkov.
- Choose the Snowflake option.
- za Ime vira podatkov, vnesite ime (npr.
snowflake). - za Vrsta povezave¸ choose the VPC connection you created earlier (
snowflake-privatelink). - za Strežnik baz podatkov, vnesite
privatelink-account-url. - za Ime baze podatkov, enter the name of your database.
- za Skladišče, enter the name of a running Snowflake warehouse.
- za Uporabniško ime, enter your Snowflake username.
- za Geslo, enter your Snowflake password.
- Izberite Potrdi.
- Upon successful validation, choose Ustvarite vir podatkov.
Create your first QuickSight dashboard
In this section, we cover creating a dataset in QuickSight, then using this data in a visualization. We’re using a dummy dataset that has information about fictional employees.
- za Shema, choose your schema.
- za Mize, select your tables.
- Izberite Izberite.
v Dokončajte ustvarjanje nabora podatkov section, you can determine if QuickSight imports your dataset into SPICE to improve query performance or directly queries your data each time a dashboard is loaded. For more information about SPICE, see Uvažanje podatkov v SPICE.
- Za to objavo izberemo Uvozite v SPICE za hitrejšo analitiko.
- Izberite Vizualiziraj.
Now that we have the schema, table, and SPICE configuration for the dataset, we can create our first visualization.
- Choose a field from the available fields list. For this post, we choose mesto.
- Choose a visualization in the Vizualne vrste
This only scratches the surface of the visualization capabilities of QuickSight. For more information, see Working with Amazon QuickSight Visuals.
Next, we cover a network configuration that allows for QuickSight to be connected to one VPC with AWS PrivateLink in another VPC, and use VPC peering to allow QuickSight to use the AWS PrivateLink connection.
QuickSight connection to Snowflake via AWS PrivateLink and VPC peering within the same Region
In this section, we show you how to connect to Snowflake with QuickSight with two VPCs peered and AWS PrivateLink. The following diagram illustrates the solution architecture.
Nastavite peering VPC
First, we create the VPC peering connection from the requesting VPC.
- o Peering povezave page of the Amazon VPC console, choose Ustvari peering povezavo.
- za Izberite lokalni VPC, s katerim želite sodelovati, choose the VPC in which you configured your Snowflake AWS PrivateLink connection.
- v Izberite drug VPC, s katerim želite sodelovati section, leave the default options for Račun in Regija (Moj račun in This Regionoz.).
- za VPC (sprejemnik), choose the VPC where your QuickSight is connected to.
- Izberite Ustvari peering povezavo.
Next, we accept the VPC connection from the accepting VPC.
- o Peering povezave page, select the connection you created.
- o Proces izberite meni Sprejmi.
- Review the information about the request. If everything looks correct, choose Da, Sprejmi.
Next, we configure DNS to resolve between the two VPCs.
- o Peering povezave page, choose your new peering connection.
- o DNS tab, check if the two options show as onemogočeno.
If they’re enabled, you can skip to the steps on creating route tables.
- o Proces izberite meni Edit DNS Settings.
This requires your VPC to have DNS host name and resolution enabled.
- Select both check boxes to allow DNS to resolve from both the acceptor and requestor VPCs.
- Izberite Shrani.
Next, create the route table entry to allow for routes to propagate between the two VPCs.
- o Tabele poti page, choose the route tables in your requesting VPC.
- o Pot izberite jeziček Edit routes.
- Add a route for the CIDR block that your peered VPC uses (for this post, 172.31.0.0/16).
- Izberite Save routes.
- Repeat for the route tables in your accepter VPC.
Configure DNS in the accepter VPC
In this section, we associate the accepter VPC that with the same private hosted zone as the requester VPC (<region>.privatelink.snowflakecomputing.com).
- On the Route 53 console, choose Hosted zones v podoknu za krmarjenje.
- Select the hosted zone
<region>.privatelink.snowflakecomputing.comIn izberite Uredi. - v VPCs to associate with the hosted zone oddelek, izberite Add VPC.
- Choose the Region and VPC ID associated with the accepter VPC.
- Izberite Shrani spremembe.
Configure Route 53 resolver inbound endpoints in the accepter VPC
To configure your Route 53 resolver inbound endpoints, complete the following steps:
- o Varnostne skupine page of the Amazon VPC console, choose Create security group.
- Vnesite ime (npr.
quicksight-doc-route53-resolver-sg) in opis. - Choose the VPC ID used in previous steps.
- Create rules that allow for DNS (port 53) over UDP and TCP from within the VPC CIDR block (for this post, 172.31.0.0/16).
- Izberite Create security group.
- Take note of the security group ID, because we now add a rule to allow traffic to the VPC endpoint security group.
Next, we set up the Route 53 inbound endpoint for this VPC.
- On the Route 53 console, choose Inbound endpoint v podoknu za krmarjenje.
- Izberite Ustvari vhodno končno točko.
- Enter a name for the endpoint (for example,
quicksight-inbound-resolver). - za VPC v regiji, choose the VPC ID for the accepter VPC.
- za Varnostna skupina, choose the security group ID you saved earlier.
- v IP naslov section, select two Availability Zones and subnets, and leave Use an IP address that is selected automatically
- Izberite Prijave se.
- Choose the inbound endpoint after it’s created.
- After the inbound endpoint has provisioned, note the two IP addresses for the resolvers.
Connect the accepter VPC to QuickSight
To start, we need to create a security group for QuickSight to allow traffic to the Route 53 resolver inbound endpoints, the VPC endpoint for AWS PrivateLink, and traffic within the local network.
- o Varnostne skupine page of the Amazon VPC console, choose Create security group.
- Vnesite ime (npr.
quicksight-snowflake-privatelink-vpc-peering-sg) in opis. - Choose the VPC ID for the accepter VPC.
- Create the following ingress rules:
-
- One rule for the local network for all TCP ports (e.g., 172.31.0.0/16).
- One rule allowing DNS traffic from the security group for the Route 53 resolver inbound endpoint for all TCP ports.
- One rule allowing DNS traffic from the security group for the Route 53 resolver inbound endpoint for all UDP ports.
- One rule allowing traffic to the security group for the VPC endpoint (located in the peered VPC).
As discussed earlier, security groups for QuickSight are different from other security groups. You must explicitly allow return traffic from the targeted security group, and the inbound rule in your security group must allow traffic on all ports. For more information, see Vstopna pravila.
Next, we modify the security group for the Route 53 resolver inbound endpoint to allow traffic from the security group we created.
- o Varnostne skupine page, search for the security group ID used for the Route 53 resolver inbound endpoint.
- Izberite Uredite vhodna pravila.
- Add rules for both DNS over UDP and DNS over TCP, using the security group ID for the security group we created for QuickSight as the source.
- Izberite Shrani pravila.
Next, modify the security group that was created for the VPC endpoint for the AWS PrivateLink connection.
- o Varnostne skupine page, search for the security group ID used for the VPC endpoint for the AWS PrivateLink connection.
- Izberite Uredite vhodna pravila.
- Add rules for both HTTPS and HTTP, using the security group ID for the security group created for QuickSight as the source.
- Izberite Shrani pravila.
Next, we set up the VPC connection in QuickSight.
- On the QuickSight console, choose the user name and choose Upravljajte QuickSight.
- V podoknu za krmarjenje izberite Manage VPC connections.
- Izberite Add a VPC connection.
- za VPC connection name¸ vnesite ime (npr.
snowflake-privatelink-vpc-peering). - za Podomrežje, choose a subnet ID that has a route table with a peering connection to the requester VPC where the AWS PrivateLink connection resides.
- za Security group ID, enter the ID of the security group created earlier.
- za Končne točke razreševalnika DNS, enter the two IPs for the inbound resolver endpoint you created.
- Izberite ustvarjanje.
Set up a Snowflake data source in QuickSight through the VPC
To set up a Snowflake data source in QuickSight, complete the following steps:
- Na konzoli QuickSight izberite Podatkovni nizi v podoknu za krmarjenje.
- Izberite Nov nabor podatkov.
- Choose the Snowflake option.
- Enter a data source name (for example,
snowflake-dataset). - Choose the VPC connection you created (
snowflake-privatelink). - za Strežnik baz podatkov, vnesite
privatelink-account-url. - za Ime baze podatkov, enter the name of your database.
- za Skladišče, enter the name of a running Snowflake warehouse.
- za Uporabniško ime, enter your Snowflake username.
- za Geslo, enter your Snowflake password.
- Izberite Potrdi.
- Upon successful validation, choose Ustvarite vir podatkov.
For steps to create a dashboard, see the earlier section, Create your first QuickSight dashboard.
In the next section, we cover a similar network configuration, with the difference being that we use cross-Region VPC peering.
QuickSight connection to Snowflake via AWS PrivateLink and VPC peering across Regions
In this section, we show you how to connect to Snowflake with QuickSight over AWS PrivateLink with two VPCs peered across Regions.
We refer to Regions generically throughout this post, denoting the Region that has the Snowflake AWS PrivateLink connection as Region A and the Region in which QuickSight is set up as Region B.
Naslednji diagram ponazarja našo arhitekturo rešitev.
Set up VPC peering between two Regions
First, we create the VPC peering connection from the requesting VPC.
- Pomaknite se na Peering povezave page on the Amazon VPC console in Region B (the Region in which you plan to use QuickSight to deploy dashboards).
- Izberite Ustvari peering povezavo.
- v Izberite lokalni VPC, s katerim želite sodelovati odsek, za VPC (vlagatelj zahteve), choose the VPC in which you have connected or intend to connect QuickSight.
- za Izberite drug VPC, s katerim želite sodelovatitako, da izberete Moj račun in Another Region.
- Choose the Region in which your Snowflake AWS PrivateLink connection exists.
- za VPC ID (Accepter), enter the VPC ID for the VPC in which your Snowflake AWS PrivateLink exists.
- Izberite Ustvari peering povezavo.
- Copy the VPC peering connection ID so we can easily locate it in the next steps (it looks like
pcx-xxxxxxxxxxxx).
Next, we accept the VPC peering connection from the Region in which you created your AWS PrivateLink connection.
- Navigate to the Amazon VPC console in Region A (where your Snowflake AWS PrivateLink connection exists).
- Search for and select the peering connection you created.
- o Proces izberite meni Sprejmi zahtevo.
- Review the information about the request. If everything looks correct, choose Da, Sprejmi.
Next, we configure DNS to resolve between the two VPCs.
- o Peering povezave page of the Amazon VPC console, choose your newly created VPC peering connection.
- o DNS tab, check if the two options show onemogočeno.
If they’re enabled, skip to the steps on creating route tables.
- o Proces izberite meni Uredite nastavitve DNS.
This requires your VPC to have DNS host name and resolution enabled.
- Select both check boxes to allow DNS to resolve from both the accepter and requestor VPCs.
- Izberite Shrani.
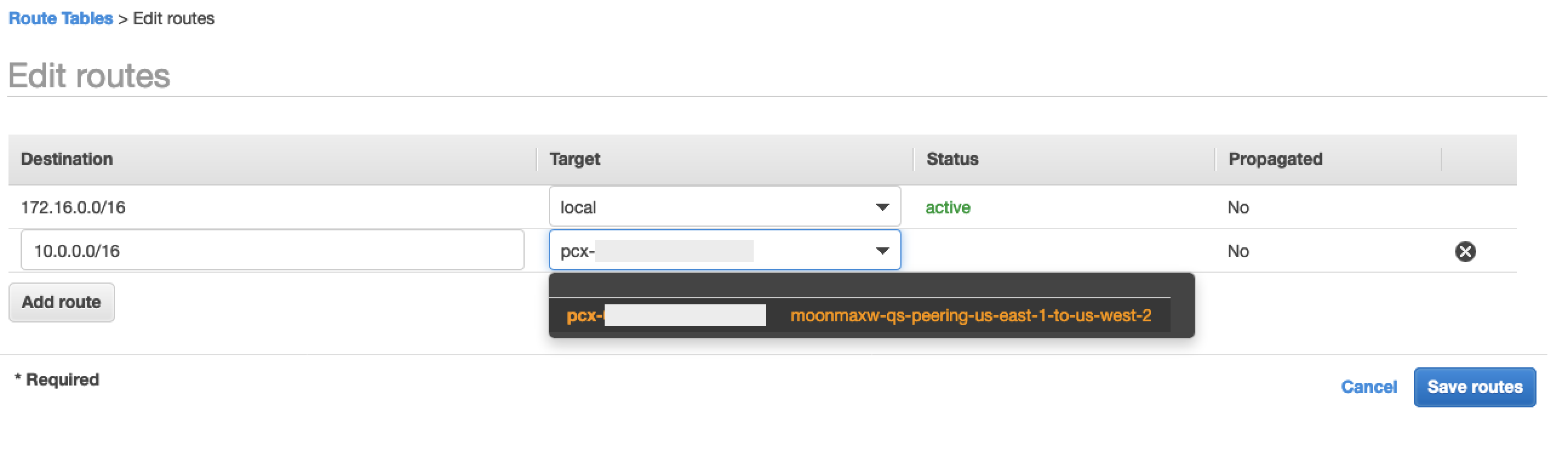
Next, we create the route table entry to allow for routes to propagate between the two VPCs for Region B.
- Navigate to the Amazon VPC console in Region B (the Region in which you plan to use QuickSight to deploy dashboards).
- V podoknu za krmarjenje izberite Tabele poti.
- Select the route tables in your requesting VPC.
- o Pot izberite jeziček Edit routes.
- Add a route for the CIDR block that your peered VPC uses (for this post, 10.0.0.0/16 is the CIDR block for the VPC in which the Snowflake AWS PrivateLink connection resides).
- Izberite Save routes.
Next, create the route table entry to allow for routes to propagate between the two VPCs for Region A.
- Navigate to the Amazon VPC console in Region A (where your Snowflake AWS PrivateLink connection exists).
- Repeat the previous steps, using the CIDR block for the peered VPC (in this post, 172.16.0.0/16).
Configure DNS in the VPC in Region B
First, we need to associate the VPC in Region B (where you deploy QuickSight) with the same private hosted zone as the VPC in Region A where your Snowflake AWS PrivateLink connection exists (<region>.privatelink.snowflakecomputing.com).
- On the Route 53 console, choose Hosted zones v podoknu za krmarjenje.
- Select the private hosted zone
<region>.privatelink.snowflakecomputing.comIn izberite Uredi. - v VPCs to associate with the hosted zone oddelek, izberite Add VPC.
- Choose the Region and VPC ID associated with the accepter VPC.
- Izberite Shrani spremembe.
Configure the Route 53 resolver inbound endpoint for your VPC in Region B
To configure the resolver inbound endpoint in Region B, complete the following steps:
- o Varnostne skupine page on the Amazon VPC console, choose Create security group.
- Vnesite ime (npr.
quicksight-doc-route53-resolver-sg) in opis. - Choose the VPC ID used in previous steps.
- Create rules that allow for DNS (port 53) over UDP and TCP from within the VPC CIDR block (for this post, 172.16.0.0/16).
- Izberite Create security group.
- Take note the security group ID, because we now add a rule to allow traffic to the VPC endpoint security group.
Next, we set up the Route 53 inbound endpoint for this VPC.
- On the Route 53 console, choose Inbound endpoint v podoknu za krmarjenje.
- Izberite Ustvari vhodno končno točko.
- Enter a name for the endpoint (for example,
quicksight-inbound-resolver). - za VPC v regiji, choose the VPC ID used in previous steps.
- za Varnostna skupina, choose the security group ID from the previous step.
- v IP naslov section, select two Availability Zones and subnets, and leave Use an IP address that is selected automatically
- Izberite Prijave se.
- Choose the inbound endpoint after it’s created.
- After the inbound endpoint has provisioned, note the two IP addresses for the resolvers.
Connect the VPC to QuickSight in Region B
To start, we need to create a security group for QuickSight to allow traffic to the Route 53 resolver inbound endpoints, the VPC endpoint for AWS PrivateLink, and traffic within the local network.
- o Varnostne skupine page of the Amazon VPC console in Region B, choose Create security group.
- Vnesite ime (npr.
quicksight-snowflake-sg) in opis. - Choose the VPC ID for the VPC where you previously created the VPC peering connection.
- Create the following ingress rules:
-
- One for the local network all TCP ports (for example, 172.16.0.0/16).
- One rule allowing DNS traffic from the security group for the Route 53 resolver inbound endpoint for all TCP ports.
- One rule allowing DNS traffic from the security group for the Route 53 resolver inbound endpoint for all UDP ports.
- One allowing traffic for all TCP ports to the CIDR block for the VPC located in Region A, where your Snowflake AWS PrivateLink connection exists (for this post, 10.0.0.0/16).
As discussed earlier, security groups for QuickSight are different from other security groups. You must explicitly allow return traffic from the targeted security group, and the inbound rule in your security group must allow traffic on all ports. For more information, see Vstopna pravila.
Next, we modify the security group for the Route 53 resolver inbound endpoint in Region B to allow traffic from the security group we created.
- o Varnostne skupine page, search for the security group ID used for the Route 53 resolver inbound endpoint.
- Izberite Uredite vhodna pravila.
- Add rules for both DNS over UDP and DNS over TCP, using the CIDR block for the VPC in Region B (for this post, 172.16.0.0/16).
- Izberite Shrani pravila.
Next, we need to modify the security group we’re using for the AWS PrivateLink connection.
- Pomaknite se na Varnostne skupine page on the Amazon VPC console in Region A.
- Search for the security group ID that is used for the VPC endpoint for the AWS PrivateLink connection.
- Izberite Uredite vhodna pravila.
- Add rules for both HTTPS and HTTP, using the CIDR Block for the VPC in Region B as the source (for this post, 172.16.0.0/16).
- Izberite Shrani pravila.
Finally, we set up the QuickSight VPC connection.
- Navigate to the QuickSight console in Region B.
- Choose the user name and choose Upravljajte QuickSight.
- V podoknu za krmarjenje izberite Manage VPC connection.
- Izberite Add a VPC connection.
- za VPC connection name, vnesite ime povezave (npr.
snowflake-privatelink-cross-region). - za VPC ID, choose the VPC ID of the VPC in Region B.
- za Podomrežje, choose a subnet ID from the VPC in Region B that has a route table with a peering connection to the VPC where the AWS PrivateLink connection resides.
- za Security group ID, enter the ID of the security group you created.
- za Končne točke razreševalnika DNS, enter the two IPs for the inbound resolver endpoint created earlier.
- Izberite ustvarjanje.
Set up a Snowflake data source in QuickSight through the VPC
To set up a Snowflake data source in QuickSight, complete the following steps:
- Na konzoli QuickSight izberite Podatkovni nizi v podoknu za krmarjenje.
- Izberite Nov nabor podatkov.
- Choose the Snowflake option.
- Enter a name for your data source (for example,
snowflake-dataset). - Choose the VPC connection you created (
snowflake-privatelink). - za Strežnik baz podatkov, vnesite
privatelink-account-url. - za Ime baze podatkov, enter the name of your database.
- za Skladišče, enter the name of a running Snowflake warehouse.
- za Uporabniško ime, enter your Snowflake username.
- za Geslo, enter your Snowflake password.
- Izberite Potrdi.
- Upon successful validation, choose Ustvarite vir podatkov.
For steps to create a dashboard, see the earlier section, Create your first QuickSight dashboard.
For our last configuration, we cover how to set up a QuickSight connection to Snowflake without AWS PrivateLink.
QuickSight connection to Snowflake without AWS PrivateLink
In this section, we show you how to connect to Snowflake with QuickSight without using AWS PrivateLink.
- Na konzoli QuickSight izberite Podatkovni nizi v podoknu za krmarjenje.
- Izberite Nov nabor podatkov.
- Choose the Snowflake option.
- Enter a data source name (for example,
snowflake-dataset). - Leave the connection type as Javno omrežje.
- za Ime baze podatkov, enter the name of your database.
- For your database server, enter the URL you use to log in to your Snowflake (
xxxxxxxx.snowflakecomputing.com). - za Skladišče, enter the name of a running Snowflake warehouse.
- za Uporabniško ime, enter your Snowflake username.
- za Geslo, enter your Snowflake password.
- Izberite Potrdi.
- Izberite Ustvarite vir podatkov.
For steps to create a dashboard, see the earlier section, Create your first QuickSight dashboard.
Čiščenje
If your work with QuickSight, Snowflake, and PrivateLink is complete, remove your Route53 resolver inbound endpoint, Route 53 private host zoneIn Končna točka VPC for Snowflake in order to avoid incurring additional fees.
zaključek
In this post, we covered four scenarios for connecting QuickSight to Snowflake as a data source using AWS PrivateLink for connectivity in three different scenarios: the same VPC, with VPC peering in the same Region, and with VPC peering across Regions. We also covered how to connect QuickSight to Snowflake without AWS PrivateLink.
After you set up the data source, you can gain further insights from your data by setting up ML Insights in QuickSight, set up graphical representations of your data using QuickSight slikeali pridružite data from multiple datasets, as well as all other QuickSight features.
O Author
 Maxwell Moon is a Senior Solutions Architect at AWS working with Independent Software Vendors (ISVs) to design and scale their applications on AWS. Outside of work, Maxwell is a dad to two cats, is an avid supporter of the Wolverhampton Wanderers Football Club, and is patiently waiting for a new wave of ska music.
Maxwell Moon is a Senior Solutions Architect at AWS working with Independent Software Vendors (ISVs) to design and scale their applications on AWS. Outside of work, Maxwell is a dad to two cats, is an avid supporter of the Wolverhampton Wanderers Football Club, and is patiently waiting for a new wave of ska music.
 Bosco Albuquerque is a Sr Partner Solution Architect at AWS and has over 20 years of experience in working with database and analytics products, from enterprise database vendors, and cloud providers and has helped large technology companies in designing data analytics solutions as well as led engineering teams is designing and implementing data analytics platforms and data products.
Bosco Albuquerque is a Sr Partner Solution Architect at AWS and has over 20 years of experience in working with database and analytics products, from enterprise database vendors, and cloud providers and has helped large technology companies in designing data analytics solutions as well as led engineering teams is designing and implementing data analytics platforms and data products.
- '
- "
- 100
- 11
- 7
- 9
- dostop
- Račun
- Dodatne
- vsi
- Dovoli
- Amazon
- analitika
- aplikacije
- Arhitektura
- razpoložljivost
- AWS
- meja
- poslovni
- Poslovna inteligenca
- klic
- Mačke
- Cloud
- klub
- Koda
- Podjetja
- povezave
- Povezovanje
- Ustvarjanje
- Armaturna plošča
- datum
- Podatkovna analiza
- Baze podatkov
- Oblikovanje
- dns
- urednik
- Zaposleni
- Končna točka
- Varnost končne točke
- Inženiring
- Podjetje
- Razširi
- Lastnosti
- pristojbine
- Področja
- prva
- nogomet
- Naprej
- polno
- Zelen
- skupina
- visoka
- Kako
- Kako
- HTTPS
- IAM
- identiteta
- Vključno
- Podatki
- vpogledi
- integracija
- Intelligence
- interaktivno
- IP
- IP naslov
- IT
- velika
- Led
- Limited
- vrstica
- LINK
- Seznam
- lokalna
- premikanje
- Glasba
- Imena
- ostalo
- mreža
- Ponudbe
- Odpre
- Možnost
- možnosti
- Da
- Ostalo
- partner
- Geslo
- performance
- Platforme
- pristanišča
- zasebna
- Izdelki
- javnega
- objavijo
- evidence
- Zahteve
- vir
- viri
- Pot
- pravila
- tek
- Lestvica
- Zaslon
- Iskalnik
- varnost
- izbran
- Brez strežnika
- nastavite
- nastavitev
- Enostavno
- So
- Software
- rešitve
- Začetek
- shranjevanje
- poddomene
- uspešno
- podpora
- Površina
- Tehnologija
- Vir
- čas
- Prometa
- ui
- vrednost
- prodajalci
- Poglej
- Virtual
- vizualizacija
- Skladišče
- Wave
- spletne strani
- v
- delo
- let