While legal legwork is already in progress to hold software vendors liable for delivering insecure products, actual laws and penalties are at least a decade away, says one policy expert who’ll be speaking at next week’s RSA Conference.
Greater accountability for insecure software vendors has the support of the Biden White House. However, licensing and contract protections have shielded companies whose vulnerable products have cost customers millions, according to James Dempsey, senior policy adviser/technology and governance lecturer, Stanford Program on Geopolitics/UC Berkeley Law School.
Dempsey will moderate a detailed discussion of proposed legal frameworks for software liability at this year’s RSA, giving vendors a glimpse at the liability landscape. He’ll be joined by Nick Leiserson, assistant national cyber director, cyber policy and programs, Office of the National Cyber Director; Bruce Schneier, security technologist, researcher, and lecturer, Harvard Kennedy School; and Chinmayi Sharma, associate professor, Fordham Law School.
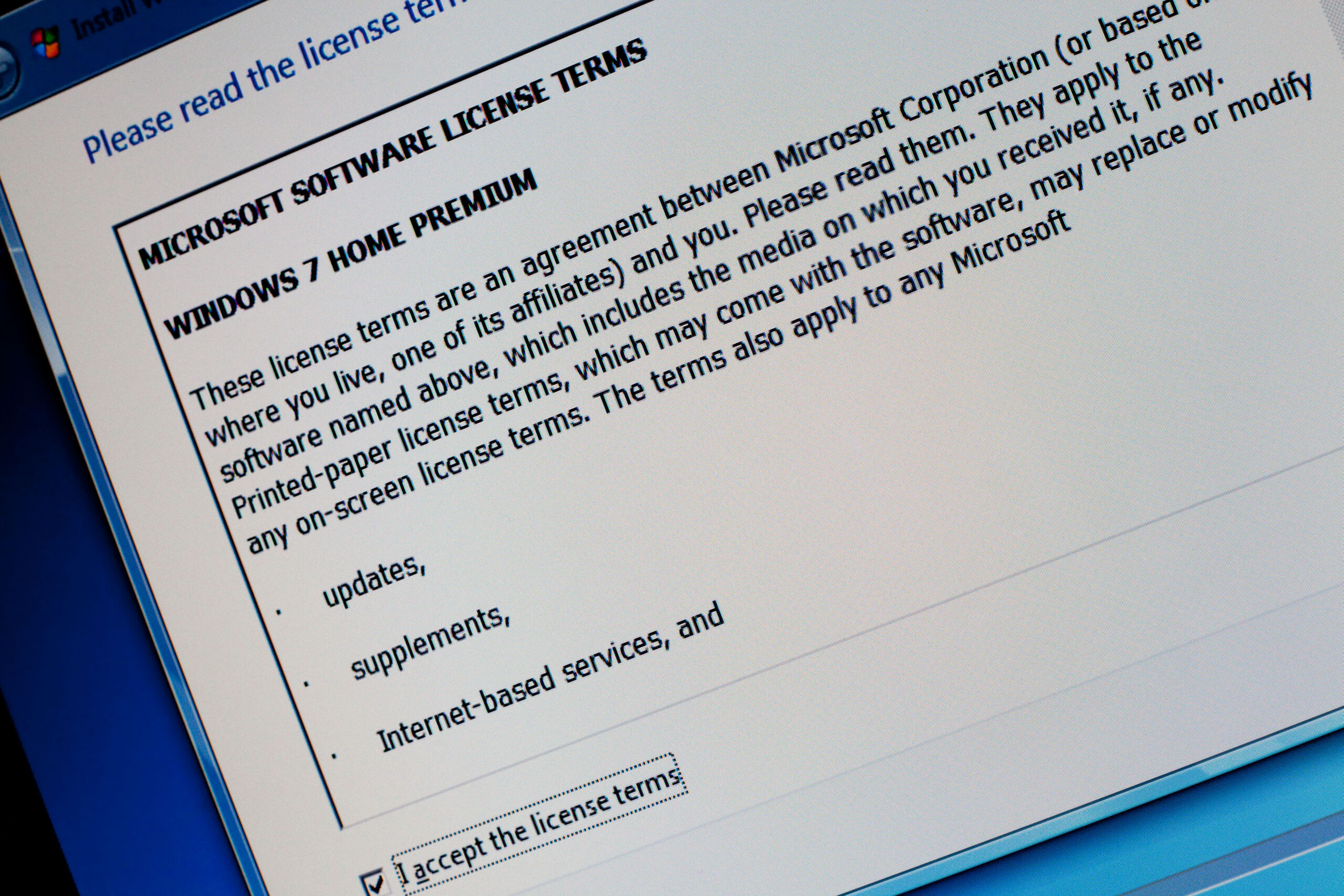
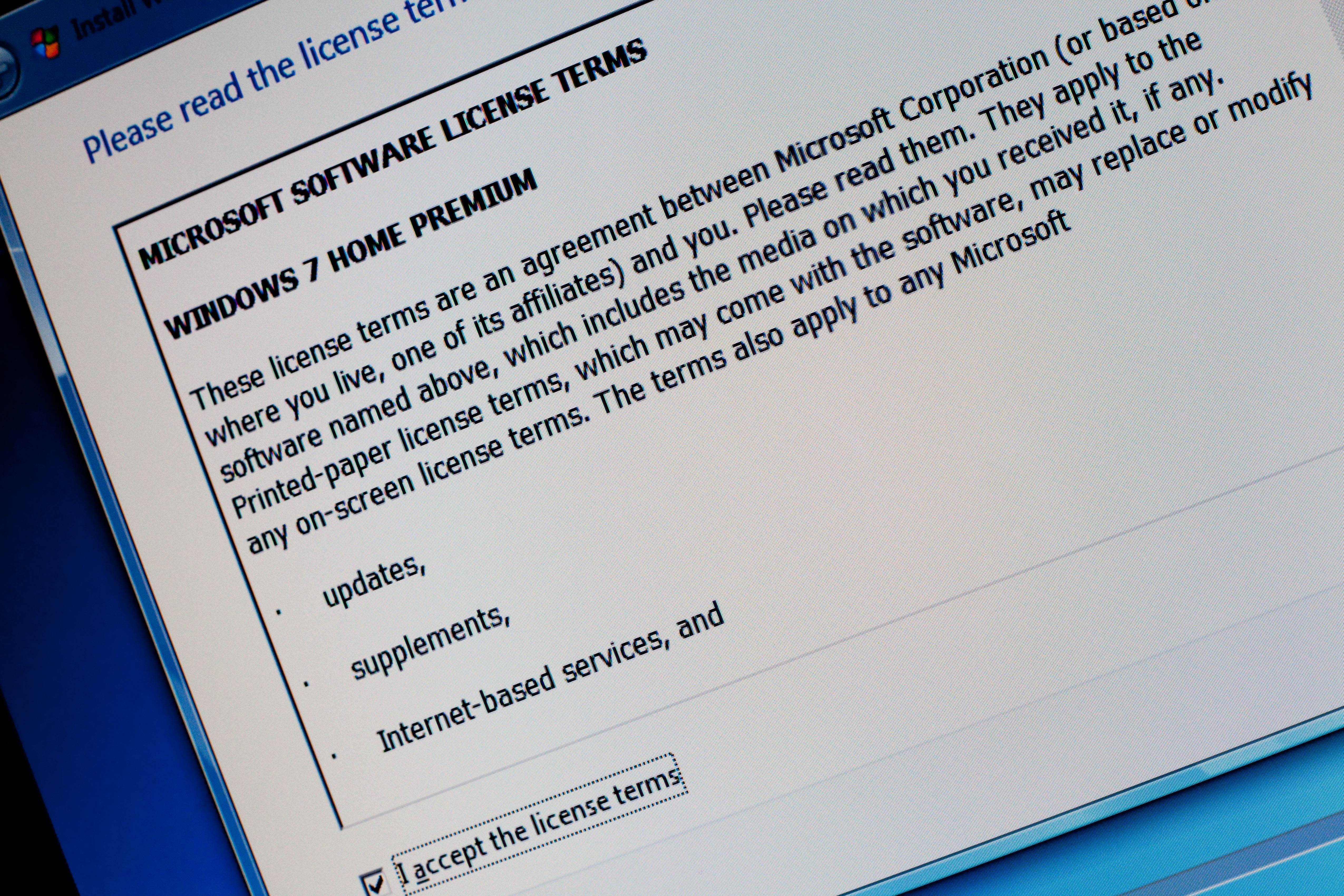
“Right now, almost all software developers have language in their licenses or other contracts or terms of service in which they disavow any liability for any flaws in their products,” Dempsey explains.
He uses the example of the Microsoft license on his own laptop to illustrate.
“For example, the Microsoft license for the operating system on my laptop says: ‘You may not under this limited warranty, under any other part of this agreement, or under any theory, recover any damages or other remedy, including lost profits or direct, consequential, special, indirect, or incidental damages,'” Dempsey tells Dark Reading. “The damage exclusions and remedy limitations in this agreement apply even if Microsoft knew or should have known about the possibility of the damages.”
That’s how vendors have been evading legal liability for their customer’s damages, and in some cases, collecting cyber insurance payouts instead.
Progress Software, whose vulnerable MOVEit file transfer software led to the breach of more than 600 organizations and the compromise of the personal information of more than 40 million people, has so far evaded liability for its customer losses. Instead, Progress filed an 8-K form with the Securities and Exchange Commission that outlined the company’s intent to collect on its full $15 million cyber-insurance policy coverage.
While there is a class-action consumer rights litigation against Progress Software for negligence and breach of contract, there are no legal protections for its customers, which in other industries could be enforced under an agreed upon legal “standard of care,” according to a recent paper, “Standards for Software Liability: Focus on the Product for Liability, Focus on the Process for Safe Harbor,” published by Dempsey in Lawfare. The paper outlines Dempsey’s theory for the right path toward holding vendors legally liable for the cybersecurity of their products.
Okta is another software vendor that has exposed its customers to cyberattacks — and losses. September cyberattacks against Caesars Entertainment and MGM Resorts used Okta as an initial attack vector. Losses related to the cyberattacks at the hospitality giants racked up hundreds of millions in costs; both in lost earnings, as well as ransomware payouts.
By the end of 2023 Okta confirmed that an unauthorized user was able to gain access to data on 100% of its customers.
Why Strong Software Developer Liability Protections Also Matter
Holding developers liable for knowingly producing insecure tools requires carefully considered guidelines for what is a reasonable level of cybersecurity to expect from a software vendor in order to determine egregious outliers, Dempsey explained.
“Because there is general agreement that the manufacturers of software should not be made insurers of their products but rather should be liable only when a product is unreasonably secure, getting software liability right turns a lot on defining a standard of care,” Dempsey’s Lawfare article read.
This standard would include defects analysis already widely used in products liability law, the article added.
Dempsey also advocates a software developer “safe harbor” for hard-to-detect flaws. “For that, I would turn to a set of robust coding practices,” Dempsey wrote.
Dempsey tells Dark Reading the Biden Administration realizes legislation will be necessary to achieve its goal of holding insecure software developers liable, which he adds they also understand is a long shot: “They see this as a 10-year issue.”
Dempsey will moderate a detailed discussion of proposed legal framework for software liability on Monday, May 6, during RSA in San Francisco at 8:30 a.m. PT, giving vendors a glimpse at the liability landscape to come.
- SEO Powered Content & PR Distribution. Get Amplified Today.
- PlatoData.Network Vertical Generative Ai. Empower Yourself. Access Here.
- PlatoAiStream. Web3 Intelligence. Knowledge Amplified. Access Here.
- PlatoESG. Carbon, CleanTech, Energy, Environment, Solar, Waste Management. Access Here.
- PlatoHealth. Biotech and Clinical Trials Intelligence. Access Here.
- Source: https://www.darkreading.com/cyber-risk/software-security-too-little-vendor-accountability-experts-say
- :has
- :is
- :not
- $UP
- 2023
- 30
- 40
- 6
- 8
- a
- Able
- About
- access
- Access to data
- According
- accountability
- Achieve
- actual
- added
- Adds
- administration
- advocates
- against
- agreed
- Agreement
- All
- almost
- already
- also
- an
- analysis
- and
- Another
- any
- Apply
- ARE
- article
- AS
- Assistant
- Associate
- At
- attack
- away
- BE
- because
- been
- Berkeley
- biden
- Biden Administration
- both
- breach
- Bruce
- but
- by
- Caesars
- care
- carefully
- cases
- Coding
- collect
- Collecting
- come
- commission
- Companies
- company
- compromise
- Conference
- CONFIRMED
- consequential
- considered
- consumer
- Consumer Rights
- contract
- contracts
- Cost
- Costs
- could
- customer
- Customers
- cyber
- cyberattacks
- Cybersecurity
- damage
- damages
- Dark
- Dark reading
- data
- decade
- defining
- delivering
- detailed
- Determine
- Developer
- developers
- direct
- Director
- discussion
- during
- Earnings
- end
- enforced
- Entertainment
- Ether (ETH)
- Even
- example
- exchange
- Exchange Commission
- expect
- expert
- experts
- explained
- Explains
- exposed
- far
- File
- filed
- flaws
- Focus
- For
- form
- Framework
- frameworks
- Francisco
- from
- full
- Gain
- General
- getting
- giants
- Giving
- Glimpse
- goal
- governance
- guidelines
- harbor
- harvard
- Have
- he
- his
- hold
- holding
- hospitality
- House
- How
- However
- HTTPS
- Hundreds
- hundreds of millions
- i
- if
- illustrate
- in
- In other
- incidental
- include
- Including
- industries
- information
- initial
- insecure
- instead
- insurance
- insurers
- intent
- issue
- ITS
- james
- joined
- jpg
- knew
- knowingly
- known
- landscape
- language
- laptop
- Law
- Laws
- least
- lecturer
- Led
- Legal
- legally
- Legislation
- Level
- liability
- liable
- License
- licenses
- Licensing
- limitations
- Limited
- Litigation
- little
- ll
- Long
- losses
- lost
- Lot
- made
- Manufacturers
- Matter
- May..
- Microsoft
- million
- millions
- moderate
- Monday
- more
- my
- National
- necessary
- next
- next week
- nick
- no
- now
- of
- Office
- OKTA
- on
- ONE
- only
- operating
- operating system
- or
- order
- organizations
- Other
- outlined
- outlines
- own
- Paper
- part
- path
- payouts
- penalties
- People
- personal
- personal information
- plato
- Plato Data Intelligence
- PlatoData
- policy
- possibility
- practices
- process
- producing
- Product
- Products
- Professor
- profits
- Program
- Programs
- Progress
- proposed
- published
- ransomware
- rather
- Read
- Reading
- reasonable
- recent
- Recover
- related
- requires
- researcher
- Resorts
- right
- rights
- robust
- rsa
- rsaconference
- s
- safe
- San
- San Francisco
- say
- says
- schneier
- School
- secure
- Securities
- Securities and Exchange Commission
- security
- see
- senior
- September
- service
- set
- Sharma
- shot
- should
- So
- so Far
- Software
- Software Developers
- software security
- some
- speaking
- special
- standard
- stanford
- strong
- support
- system
- technologist
- tells
- terms
- terms of service
- than
- that
- The
- their
- theory
- There.
- they
- this
- this year
- to
- too
- tools
- toward
- transfer
- TURN
- turns
- unauthorized
- under
- understand
- upon
- used
- User
- uses
- vendor
- vendors
- Vulnerable
- warranty
- was
- week
- WELL
- What
- What is
- when
- which
- white
- White House
- WHO
- whose
- why
- widely
- will
- with
- would
- wrote
- year
- you
- zephyrnet